______ _ | ____| /\ | | | |__ _ __ ___ _ __ ___ / \ ___| |__ ___ ___ | __| '__/ _ \| '_ ` _ \ / /\ \ / __| '_ \ / _ \/ __| | | | | | (_) | | | | | | / ____ \\__ \ | | | __/\__ \ |_| |_| \___/|_| |_| |_| /_/ \_\___/_| |_|\___||___/ H O M E <-- B A C K Meow > _
(A video of the walk through can be found at the end of the article)
Difficulty – Very Easy
Actions:
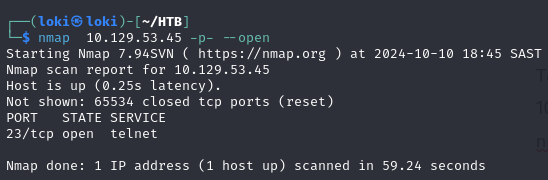
1. To get the flag open up nmap and scan the IP using nmap 10.129.53.45 -p- –open or just nmap 10.129.53.45 or another popular flag is -sV to get the service version running on the open ports using nmap 10.129.53.45 -sV (go and read up on nmap and the different flags)
You will see a response such as below showing that port 23 is open: (Port 23 is used to telnet to a machine but it transmits data in clear text and should not be used in production)
Results from the NMAP scan:
2. Now use telnet to connect to the server: (telnet IP_Address)
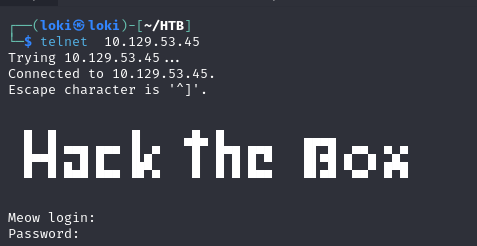
3. You get prompted to login to the server, try the usual usernames like root, admin, administrator. In this case just logging in with root and pressing enter logged us in without a password
4. Type whoami to check if you are infact the root user.
5. Type ls to show a list of files and folders and you will see the flag.txt file. Run cat flag.txt to retrieve the flag and copy / paste it as your answer.